AI-Powered 360° Security Under One Platform

Unify exposure visibility, threat detection, automated response, cyber readiness, and people empowerment under one coordinated security model.
Customer Trust
Real feedback from security teams using Logstail in daily operations.
Rating
“Logstail helped us centralize security events without adding operational noise. The platform gives our team faster context during investigations and makes daily monitoring feel much more controlled.”
Industry
Financial Services
Size
500–1,000 employees
Role
Head of Cyber Security
Why Logstail
Logstail brings security monitoring, exposure management, automation, advisory, and cyber readiness into one aligned model — helping teams move from reactive security activity to measurable resilience.
01
Security context across IT, OT, cloud, and exposed assets.
02
Automation and workflows that reduce operational drag.
03
Prioritize what meaningfully reduces exposure and impact.
04
Training, advisory, and continuous improvement programs.
Unified
Logstail
Cyber Fabric
SIEM / SOAR / Response
Assets / Risk / Priority
Academy / Labs / Teams
Governance / Maturity
Global Reach
Logstail supports teams across organizations, users, and countries with practical security visibility and operational confidence.

Offices
Users
Countries
Core capabilities
Select the capabilities your team needs across IT and OT monitoring, response, advisory, validation, exposure reduction, and workforce development.
Security Suite
Bring security monitoring, agents, SOAR automation, response workflows, and GRC into one suite for IT and OT resilience.
AI Optimization
Enhance prioritization, triage, investigation, automation, response, and resilience workflows with AI-assisted optimization.
Exposure
Discover exposed assets, understand external risk, and prioritize remediation before exposure turns into business impact.
Readiness
Build internal capability and cyber resilience through guided learning, practical labs, and structured readiness programs.
Advisory
Align cybersecurity priorities with business needs through practical strategy, governance, compliance, resilience, and improvement planning.
Validation
Validate defenses, test resilience, and uncover meaningful gaps through realistic offensive security exercises.
In focus
Build capability through practical training, reduce external risk through clearer internet-facing asset visibility, and accelerate response through automation.
SOAR
Streamline repetitive security operations through orchestration, automated playbooks, and coordinated response workflows.
Exposure Management
Discover internet-facing assets, understand external risk, and prioritize remediation efforts that materially reduce exposure.
Academy
Build team capability through lab-based learning, scenario-driven exercises, and structured skill development.
Logstail News
Explore technical insights, security guidance, product updates, and field perspectives across operations, exposure management, training, and OT security.

December 2, 2025
Introduction Black Friday used to mean camping outside a store […]
Read more →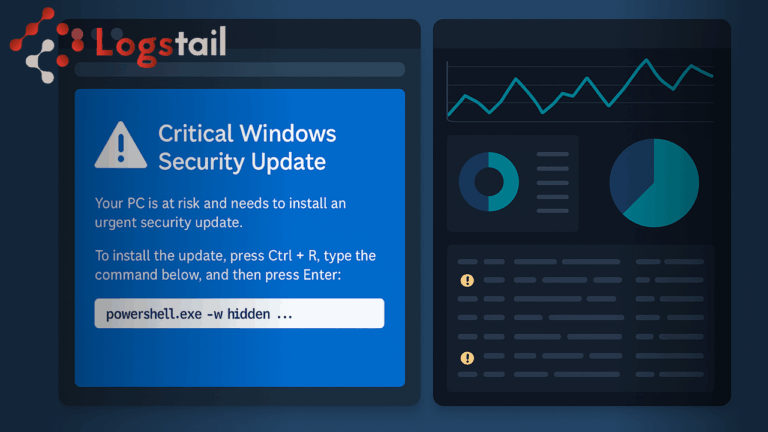
December 2, 2025
Introduction A new campaign called JackFix is using fake adult […]
Read more →
November 21, 2025
Phishing has quietly become the operating system of cybercrime in […]
Read more →