September 1, 2022
Borat RAT Malware: A multi-dimensional cyber-attack
Introduction
Generally, a RAT (Remote Access Trojan) is a type of malware that is designed to allow a hacker to remotely control a computer. Additionally, some types can even harm the computer in more ways. One of the most common ways is installing a keylogger, a type of spyware that can record keystrokes. Borat RAT is a new type of RAT malware that has surfaced very recently. Its name is inspired by the 2006 comedy “Borat”. Below, we explain what this can do to a computer and why many consider it a particularly dangerous cyber-attack.
What is Borat RAT
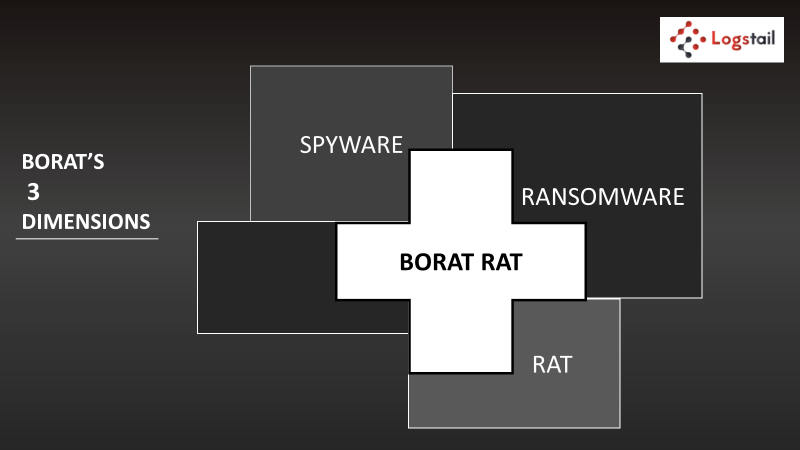
Borat RAT is a type of RAT malware that can do a lot of damage to a computer combining RAT, spyware and ransomware capabilities. Initially, it starts as a common RAT attack, which means that it gives the threat actor remote control over a computer. From there, it provides them with dashboards and gives them the opportunity to infect the computer systems with ransomware and DDoS attacks.
Borat RAT can damage a system in many different ways which can vary from annoying to extremely dangerous. Ransomware has been one of the most common attacks for a very long time and DDoS is very usual, too. These two attacks combined can be a serious problem for a company.
Other malware activities that Borat RAT can perform include keylogger installation and the ability to steal credential from browsers. They also include audio and webcam recording, a module that can connect important information and a reverse proxy for the purpose of protecting the hacker. The “annoying” features of the malware can include switching the monitor or webcam off and on, hiding desktop features or playing unwanted audio.
A Borat RAT infection can happen through different means. These include e-mails (e.g. Phishing) and cracked files that have been downloaded usually from untrustworthy websites.
Conclusion
To conclude, a Borat RAT attack is an exceptional cyber-attack, because it combines three different kinds of cyber-threats. Contrary to what its name indicates, this attack is not funny at all. In fact, it is very dangerous, and every company should be prepared for it. They can do this by monitoring their systems’ traffic and be ready to prevent it before it becomes a problem.
Logstail.com with the advanced systems and technologies helps you to have full control regarding the security of your systems to prevent a threat or improve a weak point. Now, it is not necessary to have engineering knowledge to build and use a log management and security analysis tool. Instead, you can turn your data into useful information easily and without many processes. Also, you can increase the performance of your infrastructure or be alerted to potential problems and take appropriate action. Sign up for a free demo to realize Logstail’s capabilities.
Logstail also offers the services needed to effectively mitigate cyber-attacks. Our rapid incident response and advisory, penetration testing and red team operations are specifically designed to help our customers reduce cyber-attack incidents. Contact us at sales@logstail.com to receive a custom quote for your business or get free advice from our team of experienced security experts.