
March 17, 2021
Which are the dangers of software supply chain attacks?

Introduction
In this article we will explain the software supply chain attacks and how dangerous are for companies, organizations, and individuals today. Also, we will suggest solutions to effectively mitigate this issue.
What is a software supply chain attack?
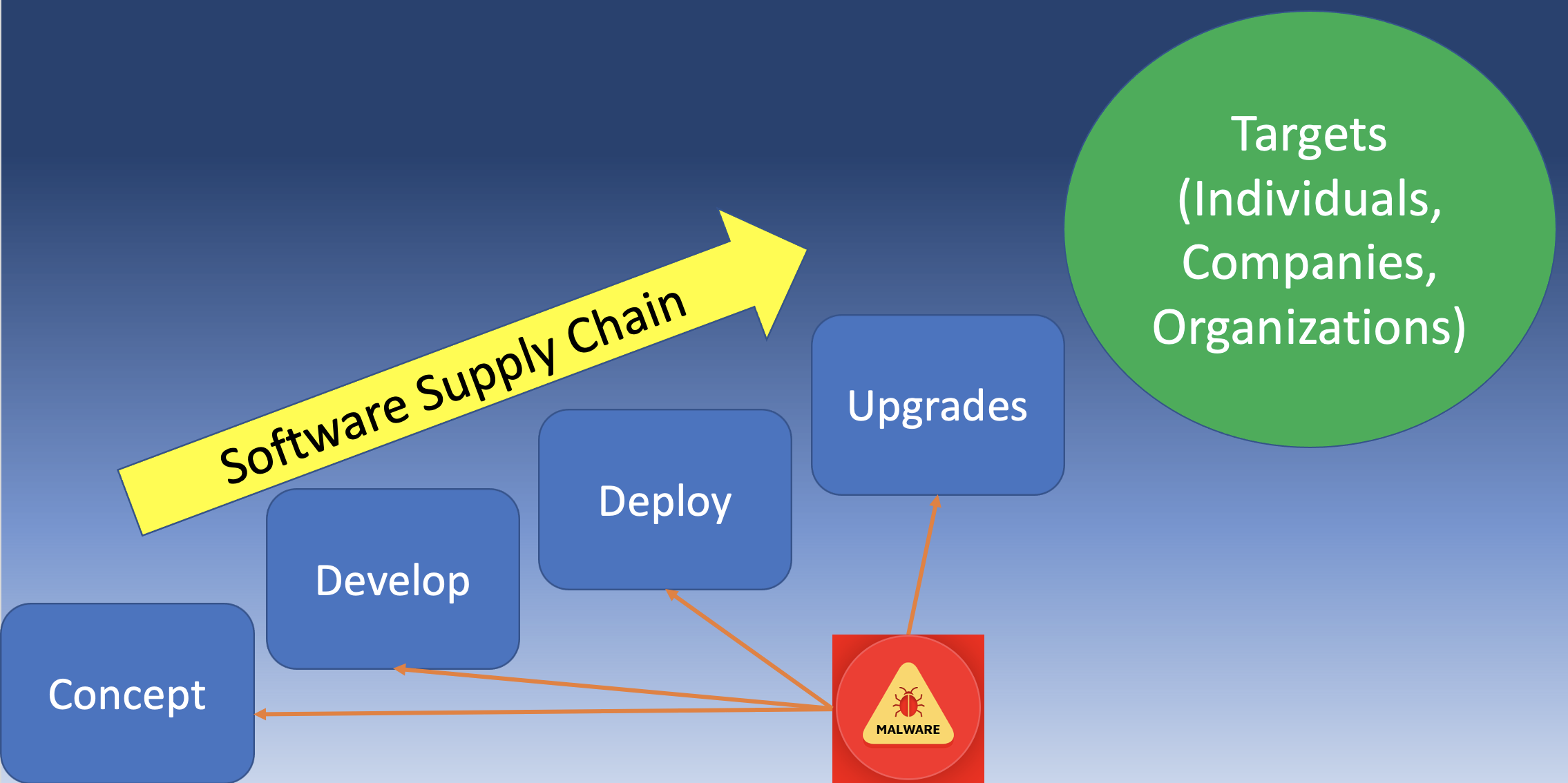
A software supply chain attack is an attack when a malicious actor succeeds in changing the code of third-party software that an organization or an individual is using. In other words, the compromise and implant of malicious code are accomplished before the software is delivered to the company target. They can hijack software updates or update servers, they can inject malicious code into legitimate applications or they can inject malicious code into third-party code libraries. Hackers are leveraging the compromised software to steal confidential data, gain access to a network and perform nefarious activities. We have seen cases where the hackers initially compromised heating or ventilation supplier software and then used this application to gain access to the company’s sensitive data. Any other ‘upstream’ part of an organization’s supply chain can be thus targeted, including application developers, publishers of off-the-shelf software like SolarWinds, API providers, and the open-source community. When the compromised software is delivered and installed to the company-target, the malicious user initiates his activities. These attacks have a tendency to target specific organizations, and for this reason, the attacker may be Nation-State Actors or Advanced Persistent Threats (APT). The latest example is the infamous SolarWinds attack.
What makes supply chain attacks so dangerous?
Modern software (open-source or proprietary) is usually built from many components which are homogeneous or coming from the same source. This is usually the norm because no developer can build a modern application from the scratch on their own. But this common practice of reusing code in projects, while it simplifies and accelerates application development, it creates security issues when the source of the code being reused has been compromised. Imagine a situation where a library or an API is being utilized by many software companies, it has been compromised. Automatically all these software companies and their customers are using malware-infected software. And the reality is that many organizations are not aware of this danger, because they believe that since the software is coming from a trusted source, then it is not going to pose a threat to the security of the organization. But this is a big misconception and although supply chain attacks have been around for a long time, many security professionals are only now becoming worried about this issue.
How can we prevent or mitigate software supply chain attacks?
As we have previously mentioned, these types of attacks are very dangerous because they are exploiting the trust relationship between companies and software vendors. The measures to prevent or mitigate these types of attacks are initially to review security measures of the software supplier on a regular basis. Also, it is recommended to host third-party libraries on your own server rather than importing them from the vendor’s server, because by following this practice you can control any changes and review them before implementation. Always implement software integrity checks to protect your applications against modification of third-party libraries, and incorporate security into the entire development process by having a comprehensive map of the dependencies used by your applications. Finally, be alerted to vulnerability disclosures and have a robust system for patching security bugs. Utilize Indicators of Compromise (IoC) obtained from Threat Intelligence feeds to proactively scan your network for unwanted behavior. Increase the security awareness among your organization so that every employee will become a security sensor. Monitor and analyze network traffic to ensure no unexpected connections are being made to servers outside of your network. Deploy an Incident Response Team in order to mitigate the issues as soon as possible. Develop the company’s defenses based on the principle that your systems will be breached. Cybersecurity is not just a technology problem, it’s a people, processes, and knowledge problem. So briefly, we recommend the following:
- Frequently review security measures of your software supplier
- Host any third-party libraries on your premises
- Implement software checks to ensure integrity
- Incorporate security into the entire development process (DevSecOps)
- Patch responsibly!
- Use Threat Intelligence for proactive detection of unwanted behaviour
- Develop a security awareness program for the whole company!
- Network Monitoring
- Deploy a SIEM and an Incident Response Team
[mo-optin-form id=”apacNKMngd”]
Conclusion
Supply chain attacks are not an IT problem only. Logstail is offering the full range of services required to effectively mitigate these types of attacks. From incident response and consulting, to penetration testing and read team operations .
And to complete the spectrum of services we offer to our customers in the field of Cybersecurity, we urge you to try our new platform! Our cloud-hosted solution with advanced features brings the functionality of centralized monitoring to your hands. Convert your data into actionable insights and maximize the performance of your infrastructure or be notified of potential problems and take the appropriate actions. Sign-up for a free demo in order to realize the power of Logstail!