October 5, 2020
DevSecOps and Log Management
From DevOps to SecDevOps
In the past, software development and IT teams used to be separated groups within an organization. Many problems stemmed from poor or in some circumstances no collaboration at all between these two teams during the development process. Developers wanted to deliver their work, under strict schedules. The IT staff, on the other hand, wanted to keep the IT infrastructure operating effectively. An efficient solution to bridge the gap between them was to have both developers and IT staff under the same umbrella of the software development team.
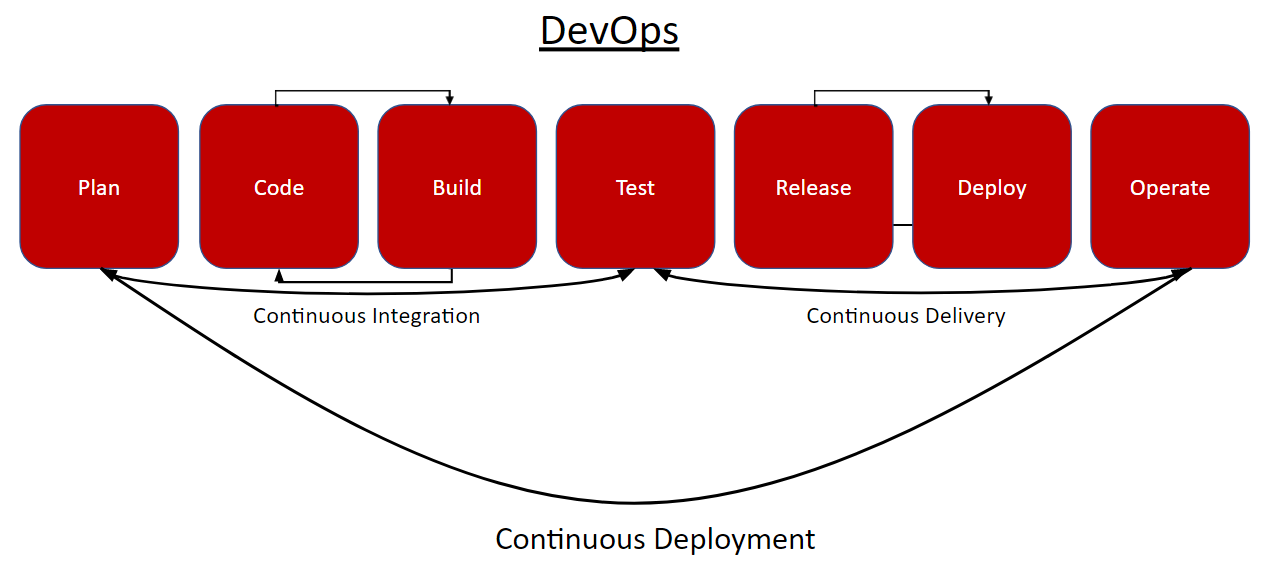
DevOps had become the best approach to incorporating effective development, IT, and quality assurance staff into software development projects. With this methodology, they managed to align their incentives to enable frequent, efficient, and reliable releases of software products. The goal of DevOps is to increase the speed of software delivery by enabling continuous collaboration, communication, automation, and integration. In recent years, DevOps has transformed the culture of organizations. It had also a positive impact on security because, in addition to Quality Assurance, the IT teammates were involved in every step of the process.
But security has become a major issue. Compromises and breaches are happening every day and corporations lose their valuable data due to software flaws. A solution that could transform the whole software process had to be found.
DevSecOps is the answer and its the latest development in the management approach and focuses on merging DevOps with cybersecurity, creating a cyclical practice for software development, technology operations, and cybersecurity.
The goal of DevSecOps is to promote the fast development of a secure codebase. Instead of prioritizing development speed or security, the DevSecOps methodology helps developers and security professionals find a healthy balance. Through the application of an agile framework, development and security teams can collaborate on a continuous basis.
DevSecOps and log management came immediately into play. Logging is extremely important in helping DevSecOps procedure, by ensuring that developers, IT staff, and security teams have the visibility and communication pipelines they need to better and faster resolve issues.
How to implement DevSecOps?
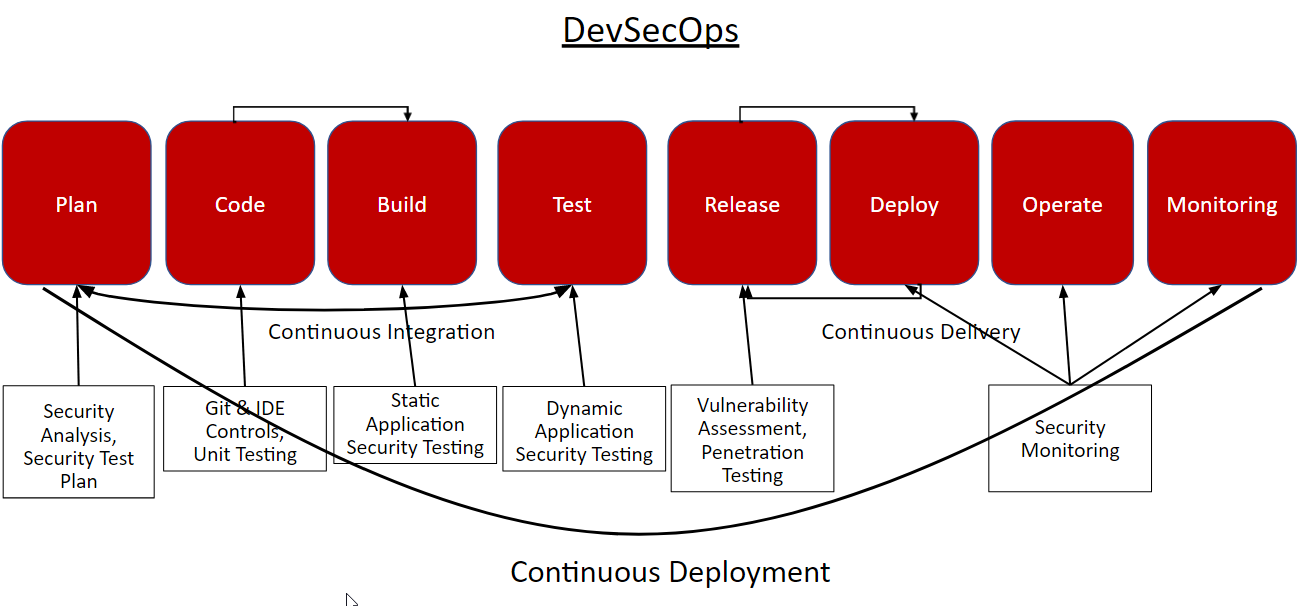
DevSecOps is more like a mentality because it demands from the people involved, to change their attitudes. For DevSecOps to function properly, the employees have to work as a team. But just like any other procedure inside a company or a corporation, there are steps to implement as an internal procedure. Briefly, the DevSecOps consists of seven steps in total:
1) Planning
2) Code Development
3) Building
4) Testing
5) Release
6) Deploy
7) Operate
8) Monitoring
Let’s start with planning which is essential for any change in the company. The management must give directions and also establish acceptance test criteria, user designs, security analysis and threat models. Code development is the second stage, where tools like Git are used to develop the code of the project. Building is the next step, where automated build tools have the task to compile code. Build automation tools offer a variety of features. And because of the emphasis on security, these tools can also automatically detect vulnerable libraries and more importantly replace them with new ones. The fourth step is testing, where the automated testing framework conducts testing of front-end, back-end, API, database, and dynamic application security testing.
Release and deployment make faster the development process and both . Infrastructure-as-code tools perform audits and configurations and ensure secure configurations across the IT infrastructure. Operation and monitoring are the last steps in the chain. The DevSecOps team deploy tools to update and secure the entire organization’s infrastructure. Also constantly monitoring and hunting for irregularities in security can save an organization from a breach. Effective monitoring is essentially the eyes of the whole team in their quest to ensure that systems are performing as intended. Hence, it is very important to implement monitoring solutions with real-time capabilities to keep a track of system performance and identify any exploits in their early stages.
How can log management help in the DevSecOps process?
This is where log management platforms like Logstail.com show their significant value. Our platform can assist every company to analyze and gain value from their logs. It is impossible for analysts to manually read the logs which are produced while applications are being tested or utilized in a production environment.
As explained above, log management plays an essential role in the successful implementation of DevSecOps. Not only in the last phases of operation and monitoring where tools like SIEM (Security Information and Event Management) play a significant role but also throughout the whole process. How? By realizing in the technical level the communication between the three roles of the personnel, the development, the operations, and the security team. Log data produced by the systems is the reference point where all parties can use to identify, respond to, and discuss security considerations. By using logs as the basis for communication, it becomes practical to operationalize DevSecOps. If a security engineer wants to explain a vulnerability with development or operations, he can refer to log data to identify the event and convey relevant information. But do not forget that the systems produce a vast amount of logs.
So, it’s important to note that simply collecting logs is not enough to facilitate DevSecOps. Being able to manage logs effectively and in a way that allows all stakeholders to see relevant trends, events, and pull out the information they need to perform a certain task, is also very important.
Of course, when we discuss about logs, we can’t ignore security. Logs provide excellent visibility into potential security considerations related to newly developed software.
And most importantly, logs come from every system in your pipeline. CI server could be used to identify anomalous code integrations. Log files from application tests and builds provide an opportunity to evaluate how software runs, and find potential vulnerabilities, before deployment. Logs from production environments can help in the detection of security issues that may arise from a running application.
In this way, logs make it possible to understand the security context of software at all stages of the DevOps pipeline, which is exactly what DevSecOps is all about.
The transition from DevOps to DevSecOps and the value of log management
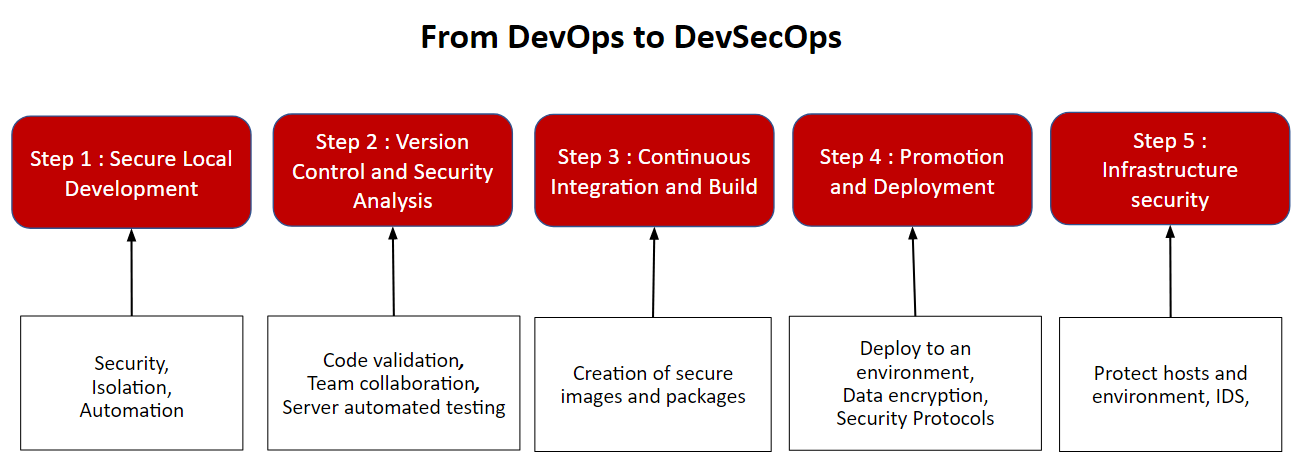
The companies cannot adopt the DevSecOps process from the first day. They need to follow a five step transition methodology in order to better adapt to the new methodology. This use case is an excellent example where companies can appreciate the value of log files. The five proposed steps to smoothly transition from DevOps to DevSecOps are:
- Secure Local Environment
- Version Control and Security Analysis
- Continuous Integration and Build
- Promotion and Deployment
- Infrastructure Security
In every transition phase, companies use different tools either automated or not. Every tool produces log files which if centralized, can provide valuable information about the adoption level of the methodology.
In Logstail, apart from the variety of applications we have already integrated and you explore here, we can integrate a variety of tools according to the company needs. Our goal is not only ready to go solution for our customers but also to help and optimize our platform based on the company’s needs!!
Conclusion
Logstail.com with its advanced features brings the functionality of centralized monitoring to your hands. You don’t have to be an engineer in order to set up and use Elasticsearch anymore. Now you can convert your data into actionable insights with just some tweaks. You can maximize the performance of your infrastructure or be notified of potential problems and take the appropriate actions. Sign-up for a free demo in order to realize the power of Logstail .
In relation to DevSecOps, if we centralize the logging of the key components, we will obtain better visibility and prevent problems in performance or security issued.