April 5, 2021
Ships and maritime industry under cyberattacks !
Introduction
Cyber risk in the maritime sector and shipping industry is difficult to be precisely determined. The reason is that the ecosystem of the maritime is huge and it may be affecting the critical infrastructure of a state. When someone mentions the maritime sector, he may refer to the ships, the ports the supply chain, or even the personnel operating in this sector. In this article, we will cover in more detail the specific risks of the maritime sector and analyze some use cases. If you want to be informed about the cybersecurity challenges at a higher level, read our relevant article. Let’s go!
Cyberattacks, Jamming and Spoofing on ships
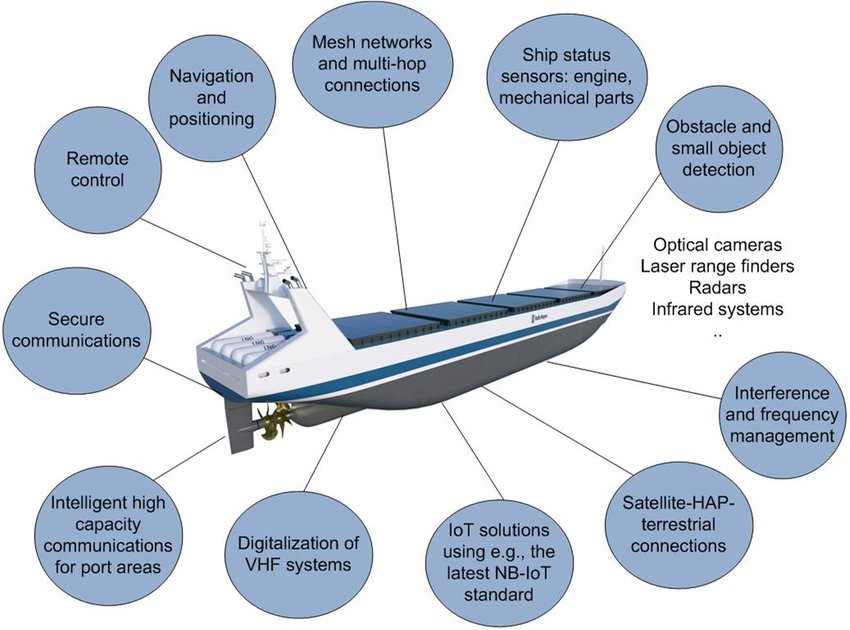
A modern ship is like a big computing platform. Hundreds of systems are cooperating to help the ship crew fulfill their mission. But as more of these systems are relying on IT or OT technology, the risk of becoming targets of a cyberattack is raising. The most vulnerable systems onboard ships are Global Positioning Systems (GPS), Automatic Identification System (AIS), Electronic Chart Display and Information System (ECDIS), Radar, and engine control.
First of all, AIS and GPS for civilian use are not encrypted or authenticated, and each has been identified as potentially vulnerable to attacks. Electronic Chart Display and Information System (ECDIS) can be also compromised in order to modify the files of the system and this can bring to very dangerous situations like displaying the vessel in a false position. A cyberattack can mislead a ship as, for example, in 2016 when two ships of the United States Navy were misdirected by malicious actors or one year later in 2017, where hackers took control of the navigation systems of a German container vessel en route from Cyprus to Djibouti for 10 hours!

Global Navigation Satellite System (GNSS) can be also susceptible to jamming and spoofing actions of malicious users that can cause significant damage to the reputation of a maritime company, to the economy of a state, or even to everyday consumers. Everyone has realized in the recent event with the blocking of the Suez canal how an incident of a single vessel can cause global effects in the world economy. GNSS is a space-based system such as the US Global Positioning System (GPS/NAVSTAR—a military capability which civilian use) or other similar system maintained by Russia, European Union, or China.
GNSS Jamming is the deliberate transmission of noise signals on relevant frequencies used by the system, in order to prevent receivers from locking on to authentic GNSS Signals. This technique requires little technical knowledge and can be conducted by acquiring low-cost hardware equipment.
GNSS Spoofing is the transmission of false GNSS satellite parameters and timing information which coerces the victim receiver into calculating incorrect positioning. GNSS spoofing is not the same as jamming, because while navigation systems sound an alarm when they recognize jamming equipment, spoofing systems create false signals that confuse even the latest of GNSS systems, leading to sometimes severe consequences. One mitigation to these type of threats related to navigational equipment is to use secondary systems based on different or older technologies, in order to correlate the outputs of both systems and take decisions if the primary systems are under attack or not.
Offices, Ports, Terminals and Supply Chains
But maritime is a rather dispersed domain and does not only refer to ships. Maritime is the offices of the company, the ports, the terminals, and of course the supply chain, either software or hardware.
After the notorious cyberattack back in 2017, when a malware had infected the IT systems of the shipping giant Maersk, shipping offices have realized how serious can a cyberattack become, and that no one is immune to cybercrime. And the more scary fact was that Maersk was not explicitly targeted, because this specific type of malware called NonPetya was created and targeted millions of systems worldwide. By that, you can imagine how devastating a similar attack would be if it was targeting the Maersk infrastructure explicitly. The attack resulted in interruptions to Maersk’s operations and terminals worldwide, costing them up to 300 million USD. Similar attacks happened in 2018 against another shipping industry giant, the COSCO company. The company’s internet connection was disrupted and the security professionals had to activate fallback plans, bringing the company back to normal operations after five days…
One of the latest publicized incidents (many of them are kept secret from companies for reputation purposes) in 2020, Carnival Corporation fell victim to a ransomware attack on its IT systems. The attackers stole certain data files related to personal data, which could result in potential claims from clients, employees, shareholders, and lead to fines imposing from regulatory agencies.
Another factor that has to be taken into consideration is the ports. They are an integral node of maritime transportation and they rely on information from both shipping lines and land-side logistics companies. Usually, old IT systems are requested to connect and exchange information with the latest technologies like the Internet of Things (IoT) resulting in making ports vulnerable. Only a fraction of the world’s shipping ports are aware of the problems and vulnerabilities, despite the fact that the regulatory framework exists in the European Union at least, where ports are considered as critical infrastructures of a state (they are called Operators of Essential Services-OES).
Finally, the supply chain threats have been analyzed in another article on our blog, but briefly, these type of attacks are particularly dangerous because they aim to exploit the trust relationships between companies and suppliers, and they are very difficult to detect because usually they are organized by state-sponsored actors, which means that they are well funded and so they spend a lot of resources in order to be stealth.
Social Media and Hybrid Threats
It is also a mistake to underestimate the impact of social media on the crew’s life at sea or back at the company offices. Ship crew heavily relies on the usage of social networking services to entertain and communicate with the outside world and families. But leakage of information on confidential shipping matters can unintentionally cause many problems, which cal lead to a marine accident or the exposure of personal and private information.
Hybrid threats are another attack vector that aims to undermine a state, frustrate its decision-making processes, stay undetected, and be difficult to attribute to a specific adversary. As a critical domain for the economy, resources, trade, transport, security, and defense, the maritime domain, including ports, finds itself a target of hybrid threats. The fact that much of the (maritime) critical infrastructure is privately owned complicates the construction of a strong and coordinated response to hybrid threats.
Due to their low-level and dispersed nature, hybrid threats can only be fully recognized by correlating information about facts or incidents that individually may seem minor but are part of a larger picture, creating what is called Situational Awareness – SA. The sharing of information on disruptions is very important, just like it is the case for cyberattacks outside the hybrid context. For adequate business continuity, the magic word here again is resilience against hybrid attacks. Risk analysis and enhancing the overall resilience of the critical maritime infrastructure with regard to cyber and hybrid threats are actions that aim to reduce risk to an acceptable level. Proper defense against hybrid threats requires all-of-society awareness and resilience and the whole of government approach.
[mo-optin-form id=”apacNKMngd”]
Conclusion
Cyber-attacks in the maritime sector will be discussed every time a major incident occurs, resulting in a loss of millions of dollars and the reputation of companies and countries. The deadline for compliance with the International Maritime Organisation’s (IMO) cybersecurity regulations has already passed. From 1st of January of 2021 maritime organizations are required to implement cybersecurity measures set out by the IMO.
In Logstail we are offering the full range of services required to effectively mitigate cyber-attacks in the maritime sector. Incident response and consulting, penetration testing, and red team operations, are altogether aiming to help our customers mitigate their cyber incidents.
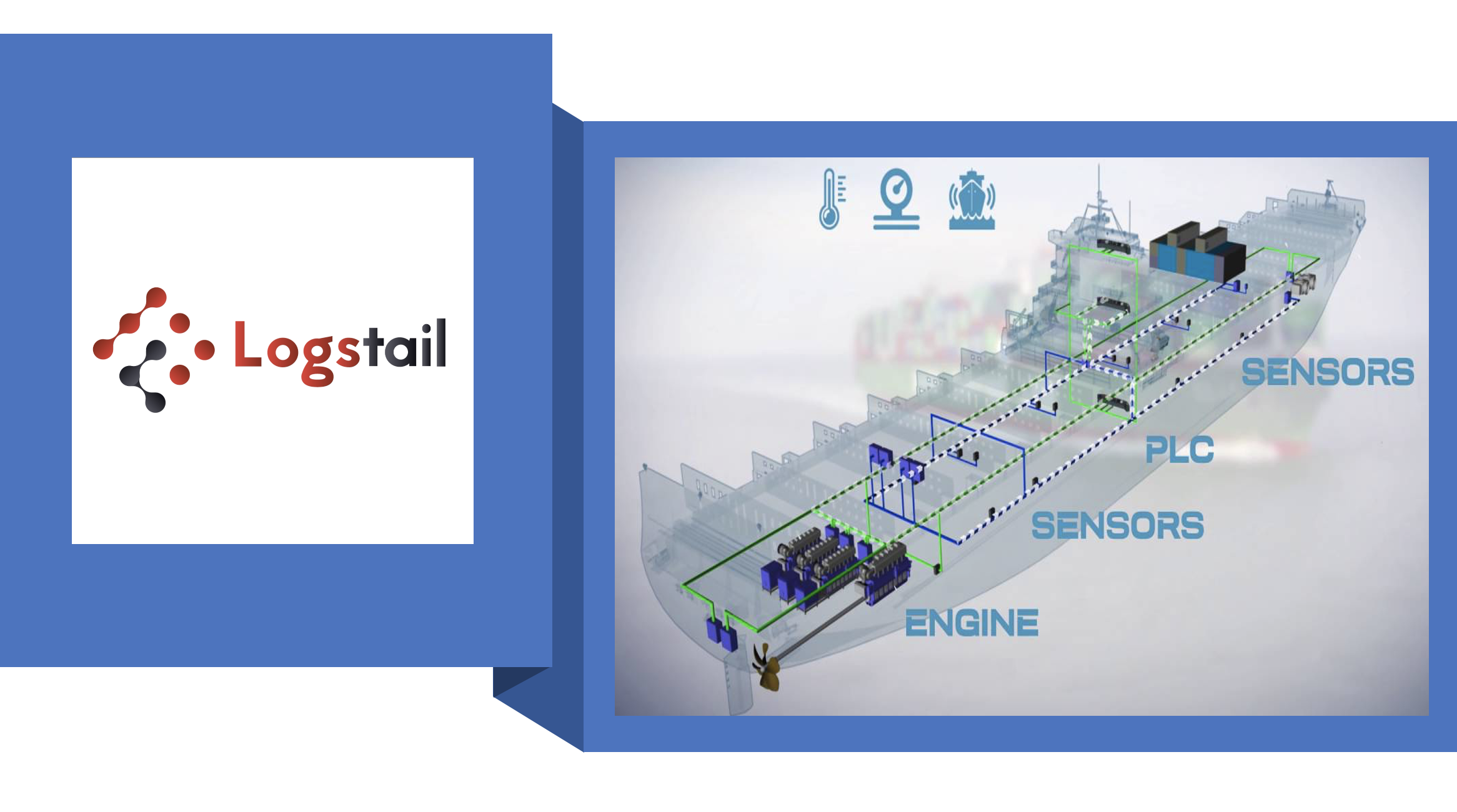
To further support our security consulting services tailored for the maritime industry, we offer to our customers our brand new log management and security platform! Logstail’s cloud-hosted solution with its advanced features brings the functionality of centralized monitoring to your hands. It covers the requirements of almost all systems referred above, whether it is the PLC or a sensor, and also with its Advanced Alerting and Machine Learning capabilities gives the crew the ability to detect threats and anomalies in the entire vessel or port infrastructure in near real-time!! Also, its reporting feature will produce scheduled or on-demand reports to offer a complete Situation Awareness (SA) to the companies from both IT and OT systems.
Very soon we will launch our cloud Security Incident and Event Management (SIEM) solution to further complement our existing services. Logstail’s team is working really hard to help its customers convert their data into actionable insights and maximize the performance of every maritime infrastructure or be notified of potential problems and take the appropriate actions. Sign-up for a free demo in order to realize the power of Logstail.