
August 5, 2022
The types of social engineering attacks and how to prevent them
Introduction
As we have already mentioned in a previous article, social engineering is one of the methods used by cybercriminals in order to break into a system. This method relies on people’s awareness of cybersecurity. Many times, the employees are not as careful as they should be with the security of their systems. This results, quite often, hackers manage to manipulate the employees in order to fall victims and give them useful information. In this article, we will analyze the types of social engineering attacks and how an organization can protect itself from them.
Social engineering attacks
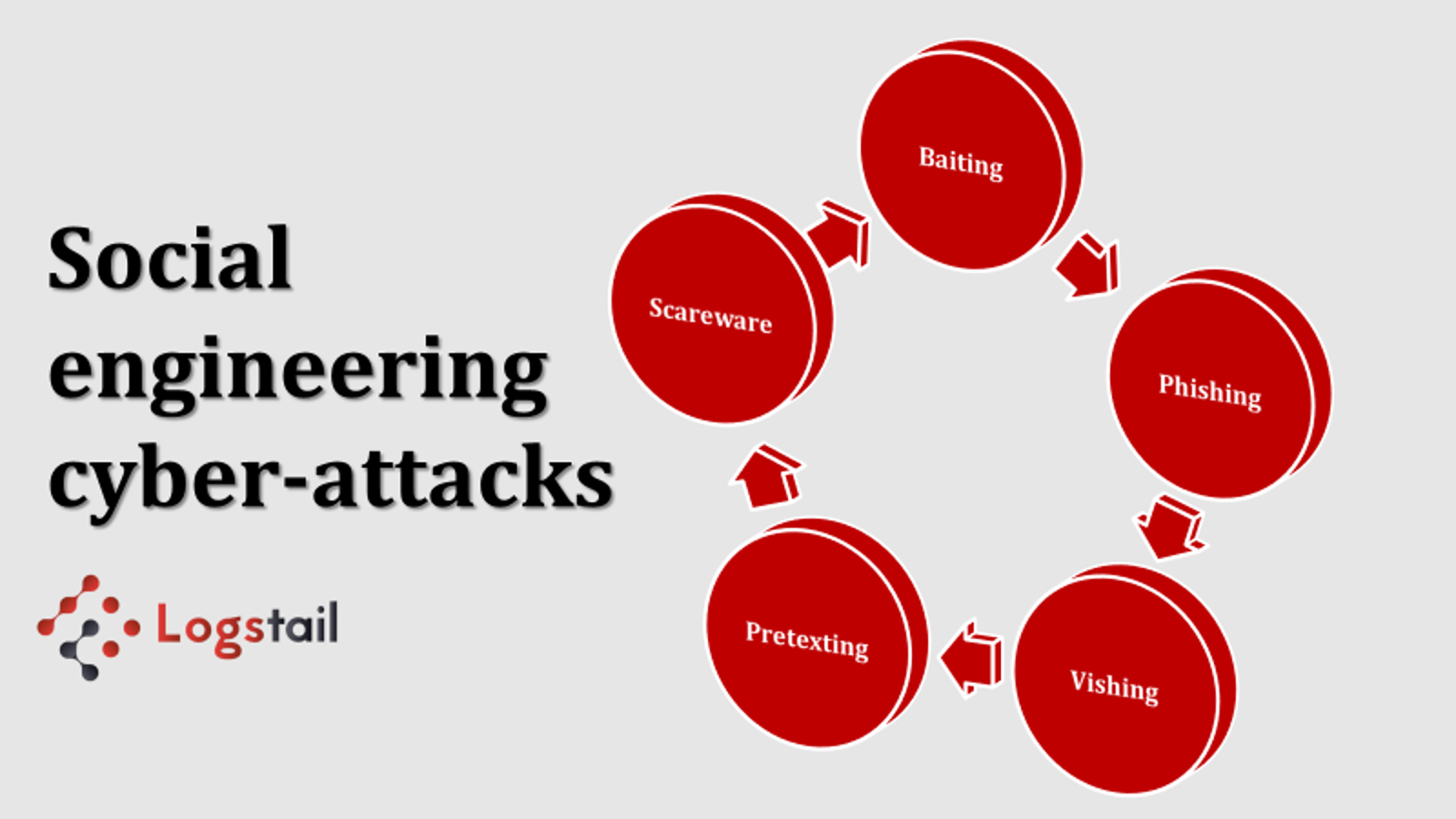
Unfortunately, there are many categories of social engineering cyber-attacks that confuse employees and extract useful confidential data from their organization. Let’s find out these types of cyber-attacks to be more informative in order to mitigate them.
Phishing Attacks
First of all, one of the most common cyber-attacks is phishing. As we have analyzed many times in previous articles, hackers who use his method of cyber-attacks, send a link (usually in email form) aiming for the employee to click on this link and succeed in penetrating their system. Thus, the employees believe that these emails are from a trustworthy person, such as a colleague of theirs, and that is why they fall into the hacker’s trap.
Vishing Attacks
As in a phishing attack, cybercriminals attempt to gain control of company’s systems and steal important files and data from them. However, hackers using this method do not send texts or emails as with phishing attacks, but they use phone calls to ask for information. Pretending for example to be someone higher in the company’s hierarchy such as a manager or some external partner, they once again manage to successfully infiltrate the business.
Baiting
In addition, another social engineering attack is Baiting. This type of cyber-attack exists in digital form as well as in physical form. This attack manipulates users by baiting them with tempting offers and generally some kind of reward to the victim. For example, a common phenomenon are the banners that appear on websites and try to make you believe that you have won a new mobile device. Their purpose is to click on them and fall into the trap of thieves. As we already mentioned, baiting also can exist in physical form such as in a form of devices like a USB stick. Many users, ignoring the dangers, try these packages either thinking they are theirs or out of curiosity. This results to hackers breaking into users’ systems and intercepting their data.
Pretexting
This type of social engineering attacks aims to extort significant information too. In order to obtain this information, the hacker tries to deceive the user by giving false personal data, for example pretending to be a colleague or an external partner. Having already gathered the necessary information he needs, the hacker can easily convince the user of his identity. This is how the criminal manages to extract confidential files, sensitive data or even user’s login codes.
Scareware
Scareware is a type of malware, which tricks users with false warnings into believing they are infected. By using spam emails or in the form of a banner on some website on the Internet, cybercriminals try to convince users to install new software, which may be malicious. With this method, they trap users with the goal of invading and infecting their systems.
Ways to prevent social engineering attacks
Employees awareness
First, one of the ways to protect a business from hackers of social engineering is to properly inform its employees to take appropriate security measures. Every employee should be trained to understand how cybercriminals work. With this training, the employee will always be suspicious of any threats so that he can avoid as many as he can. Moreover, every employee of an organization must be aware of these ways of hacking in order to be more and more careful for example with his personal login codes and personal data in general. It would be very useful for every employee to be able to be notified when he receives links, emails, or phone calls from malicious sources to avoid the dangers behind social engineering attacks.
Log management platform
It is crucial for every organization to be able to monitor its systems. In addition, it is equally important for a business to be able to manage its logs files so that it can analyze them to avoid any weaknesses. It is very easy for a business to avoid social engineering hackers if it monitors its systems on a 24/7 basis. In this way, if someone tries to break into a company’s systems, for example by sending a malicious e-mail, a log management platform will detect it. So, the IT teams will act appropriately to avoid them.
Conclusion
In conclusion, it is important for all organizations to know the types of cyberattacks because cybercriminals are constantly creating more of them. Social engineering is one of the most common methods of cyberattacks, so organizations must take precautionary measures to stay safe.
Our cloud-hosted solution with advanced features brings the functionality of centralized monitoring to your hands. Convert your data into actionable insights to maximize the performance of your infrastructure. Also, you are notified of potential problems to take the appropriate action. Sign-up for a free demo to realize the power of Logstail! Logstail will re-adjust the way you monitor your data and will help you get more meaningful insights of your technical logs, via dashboards and powerful graphs, to stay alert for all dangers.
In Logstail we are also offering the full range of services required to effectively mitigate cyber-attacks. Incident response and consulting, penetration testing and red team operations are altogether aiming to help our customers mitigate their cyber incidents. Contact us at sales@logstail.com to get a tailored offer for your business.