September 7, 2022
Types of Man-in-the-middle attacks
Introduction
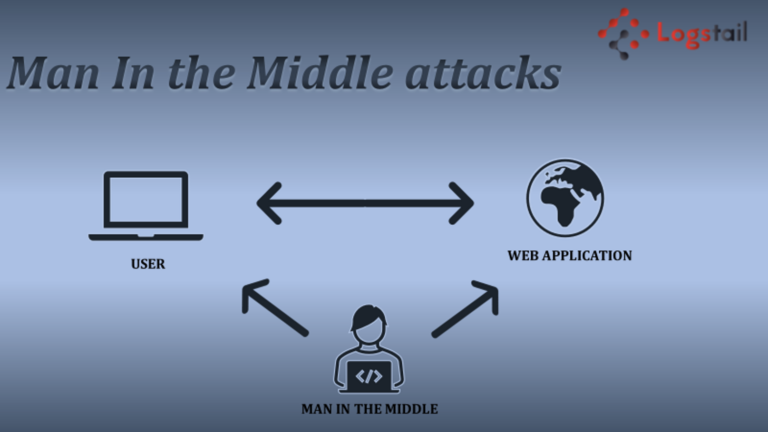
Man-in-the-middle (MITM) attacks occur when an attacker tries to get in the middle of the communication between a user and an application. These attacks are usually carried out with the purpose of the hacker stealing valuable information, often impersonating one of the parties to the conversation. The goal of ΜΙΤΜ attacks is to steal confidential information and sensitive data such as login credentials and credit card codes. Successful MITM attacks are done in two phases: Interception and Decryption. In this article, we will analyze the types of man-in-the-middle attacks in order to protect your organization against them.
1) Interception
IP Spoofing
IP Spoofing is the redirection of a selected location’s traffic created by spoofing the IP headers of TCP packets. These headers are transferred between two devices that trust each other. Using IP Spoofing, hackers create a backdoor in the victim’s systems to gain root access to the host computer.
ARP Spoofing
ARP (Address Resolution Protocol) Spoofing is used to resolve IP addresses to physical MAC (media access control) addresses on a LAN. This spoofing allows a hacker to send an address resolution protocol message to locate a MAC address over a spoofed local network by gaining the trust of the server. Thus, hackers can respond to requests that they should not be able in normal circumstances with their MAC address trial. As a result, cybercriminals have the ability to intercept valuable information to gain access to application accounts.
DNS Spoofing
Another type of man-in-the-middle attacks is DNS (Domain name system) Spoofing. Cybercriminals try to replace a legitimate IP address in DNS server records. This is how hackers manage to direct users to a fake website. DNS protocol is mapped to an IP address when a client makes a request.

2) Decryption
HTTPS Spoofing
Some experts consider that these attacks are a type of phishing attacks. Cybercriminals create a fake website pretending to be legitimate. Thus, they send a fake link trying to deceive users and break into their systems.
SSL Hijacking
SSL hijacking refers to threat actors compromising a user’s operation and pretending to be that user. The server does not know that this user is not the intended one because someone has gained authorized control. These types of Man-in-the-middle attacks are also known as session hijacking attacks or cookie jacking attacks.
SSL Stripping
SSL Stripping, also known as downgrade attack, is the method in which a hacker reduces the security of a website connection. This tactic manages to infiltrate the communications between clients and servers they connect to. Successful execution of SSL Stripping gives the hacker access to any information transferred between the user and the server.
Conclusion
In conclusion, there are a lot of types of MITM attacks and they are constantly increasing as hackers discover new tactics. Every organization should be aware of these attacks in order to protect their systems and keep their confidential data secure.
Our cloud-hosted solution with advanced features brings the functionality of centralized monitoring to your hands. Convert your data into actionable insights and maximize the performance of your infrastructure in order to be alerted of potential problems and take the appropriate actions. Sign-up for a free demo in order to realize the power of Logstail!
Logstail will re-adjust the way you monitor your data and will help you get more meaningful insights of your technical logs, via dashboards and powerful graphs, to stay alert for all dangers.
In Logstail we are also offering a full range of services required to effectively mitigate cyber-attacks such as man-in-the-middle attacks. Incident response and consulting, penetration testing and red team operations are altogether aiming to help our customers prevent their cyber incidents.