October 27, 2023
Monitor Windows Endpoints with Logstail
Monitor Windows Endpoints with Logstail
In the ever-evolving landscape of IT management, keeping a vigilant eye on Windows log events and system performance is not just a best practice but a necessity. In our latest technical exploration, we delve into the intricate realm of monitoring Windows log events and system performance using the powerful Logstail Platform. In this post, we will unravel the myriad features that make Logstail a game-changer in the world of system monitoring. From real-time event tracking to in-depth performance analysis, Logstail equips administrators with unparalleled insights, ensuring the seamless functioning and security of Windows environments. Join us on this insightful journey as we navigate the complexities of Windows event monitoring and performance optimization, leveraging the cutting-edge capabilities of the Logstail Platform.
The Crucial Role of Windows Logs and Infrastructure Metrics in Modern IT Management
Collecting Windows logs alongside infrastructure metrics is paramount in maintaining a robust and secure IT environment. Windows logs provide a detailed account of system activities, highlighting critical events, errors, and security incidents. By meticulously analyzing these logs, organizations can gain invaluable insights into the health and security of their Windows-based infrastructure. However, logs alone don’t paint the complete picture. To truly understand the performance and efficiency of the system, it is essential to complement log data with infrastructure metrics. These metrics offer quantitative measurements of system components, such as CPU usage, memory consumption, and network traffic. The synergy between Windows logs and infrastructure metrics enables IT professionals to proactively identify issues, troubleshoot problems, and optimize system performance. This holistic approach not only enhances the system’s reliability but also bolsters cybersecurity efforts by detecting and mitigating potential threats before they escalate. In an era where data is paramount, the amalgamation of logs and metrics stands as the linchpin for informed decision-making, ensuring seamless operations and fortified digital defenses.
How to start monitoring Windows with Logstail?
Embarking on the journey to monitor Windows systems using Logstail is a streamlined process that involves just a few simple steps.
- First and foremost, start by creating an account on the Logstail platform, providing you with a secure gateway to manage your monitoring activities.
- Once your account is set up, proceed to the next step by downloading the Logstail Agent, a lightweight yet powerful tool designed to collect and transmit crucial Windows log data and infrastructure metrics.
- After the download is complete, follow the user-friendly setup wizard, configuring the agent according to your specific monitoring requirements. This step involves defining which Windows log events and metrics you want to track, ensuring that you receive the most relevant and actionable insights.
- Once the agent is properly configured, you’re all set. With your Logstail agent up and running, you can effortlessly access and analyze your data through the intuitive Logstail dashboard, gaining valuable real-time insights into your Windows environment.
With these simple steps completed, you’re well-equipped to monitor your Windows systems effectively and make informed decisions to enhance performance and security.
Configure the agent to monitor Windows Endpoint
After following the guide of how to add your Logstail Token in the Logstail Agent you will need to install the below highlighted collectors:
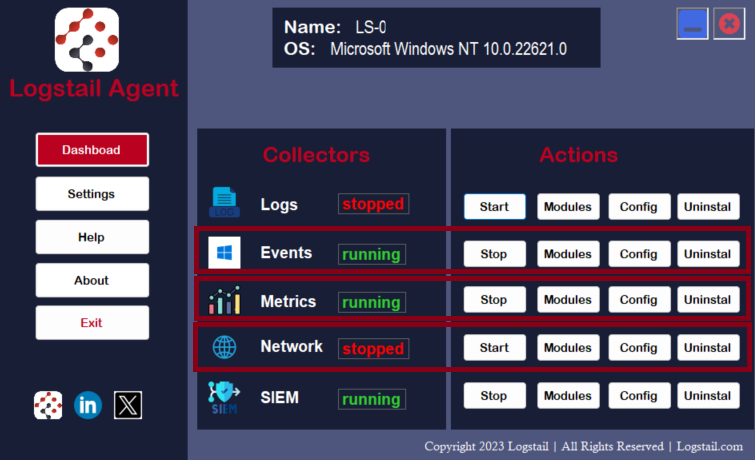
- Events Collector is specifically designed to collect and centralize Windows event logs and forward them to Logstail Platform for analysis and visualization. It acts as an agent that monitors the Windows event log system, allowing users to collect events from different event logs, filter them based on specific criteria, and send the selected events to Logstail for searching, analyzing, and visualizing the events.
- Metrics Collector is designed for collecting system and service metrics from various sources. Metrics offer quantitative data related to the performance and behavior and are crucial for monitoring the health and performance of servers, containers, databases, and other applications. Metrics collector is essential for system administrators and developers to ensure the optimal functioning of their infrastructure, identify bottlenecks, troubleshoot issues, and make data-driven decisions to improve overall performance and user experience. After installing the collector click on Modules and make sure you enable System metrics modules and Windows metrics modules.
- Network Collector is used for monitoring network traffic in real-time, capturing network packets and extracting relevant metadata from various protocols, such as HTTP, DNS, TCP, and more. Unlike traditional network monitoring tools that focus on aggregated statistics, it provides detailed insights into the communication patterns between different systems and services. It is particularly valuable for security monitoring, troubleshooting network issues, and gaining visibility into the interactions between applications. It helps network administrators and security professionals detect potential security threats, analyze network behavior, and investigate security incidents by providing granular information about network activities. If you want to gain deep visibility and insights in the network traffic related to your Windows Endpoint then make sure to install this collector too!
- SIEM Collector is a key component of Logstail Platform. It is crucial for real-time threat detection, log analysis, and incident response within an organization’s IT environment. SIEM actively monitors log files, system events, application logs, and other data sources on the host where it is installed. It performs log analysis locally, allowing for immediate detection of security incidents. Also performs integrity checking on system files and registry entries, ensuring that critical system components have not been tampered with, which is especially important for identifying signs of compromise or malware activity. Additionally, it can be configured to perform rootkit detection, providing an additional layer of security by identifying hidden or malicious software that may have compromised the host system. Furthermore, SIEM Collector offers vulnerability detection by integrating with vulnerability databases and performing periodic scans of systems and applications. It helps organizations identify and address security vulnerabilities before they can be exploited by attackers.
For enhanced visibility, in-depth analysis, and effective event correlation, integrating your system with the MITRE Framework, various compliance regulations, continuous vulnerability scanning, and file integrity monitoring is imperative. Elevate your capabilities by transitioning to our Enterprise Plan, which grants you access to a robust Security Information and Event Management (SIEM) system. With SIEM, you can delve deep into your data, leveraging the power of MITRE Framework and compliance regulations to strengthen your security posture. Moreover, SIEM empowers you to monitor your Cloud Office365 organization seamlessly, collecting and analyzing events from it. This comprehensive solution not only ensures compliance but also fortifies your defenses, allowing you to proactively respond to security threats and vulnerabilities.
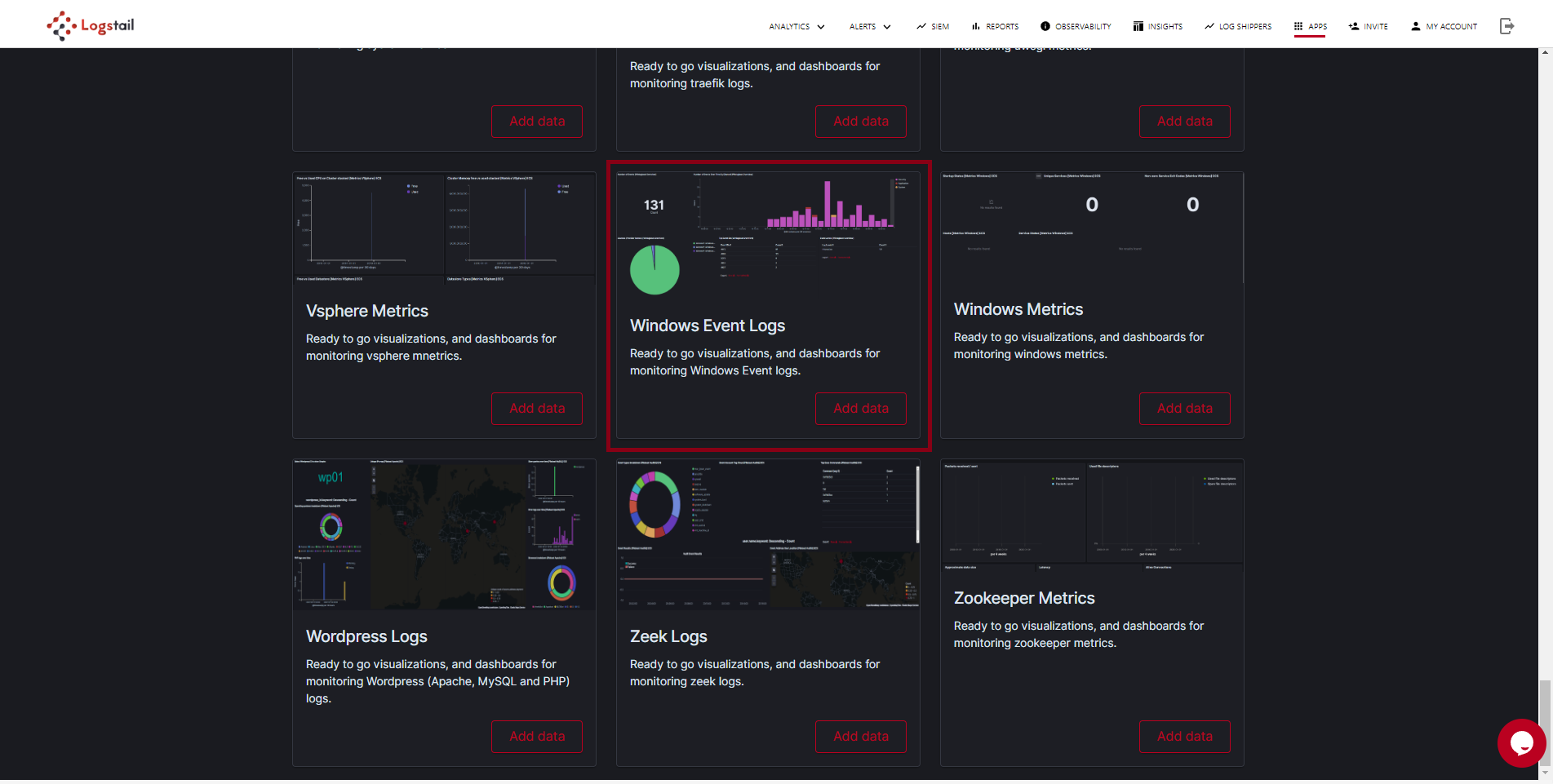
Add Logstail’s Pre-built Dashboard
After installing and starting the desired collector, it’s time to observe your collected data on the Logstail platform. Navigate to the ‘Apps‘ section from the top navigation menu specific to Logstail. Here, locate the ‘Windows Event Logs Dashboard’ and proceed to install it. This step is pivotal as it provides you with an organized and visually accessible interface to analyze your Windows event data comprehensively. By leveraging Logstail’s intuitive dashboard, you can effectively interpret system activities, security events, and performance metrics. This insightful analysis empowers you to make informed decisions, ensuring the optimal functioning and security of your Windows environment.
Observe your Data using pre-built Dashboards
Navigate to Analytics → Dashboards from top navigation menu and search for the “Windows Events [Overview]” dashboard.
Overview Dashboard
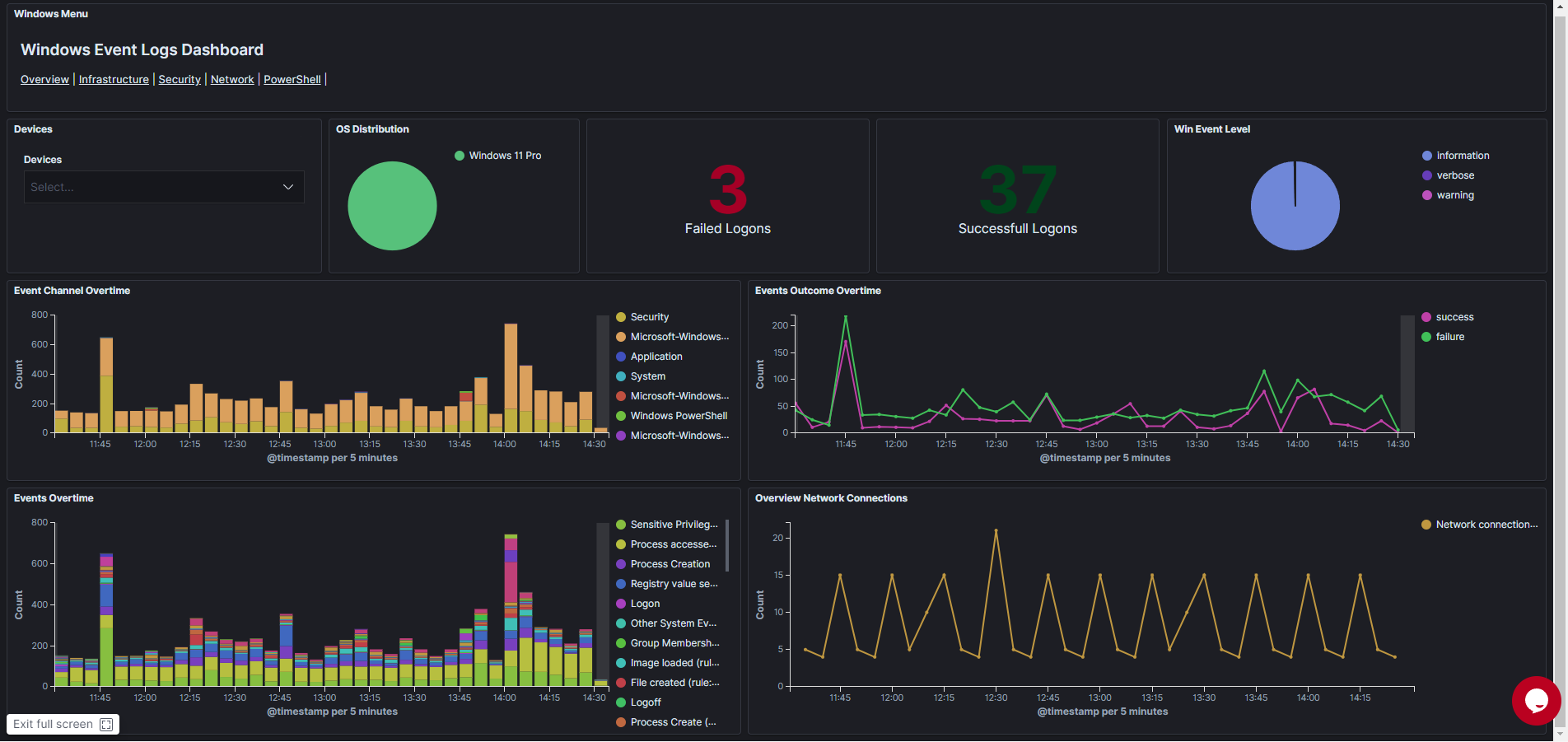
Within the overview dashboard of Logstail, you gain a detailed insight into the events collected from your Windows endpoints. This includes crucial metrics such as Failed and Successful Logons, as well as the criticality level of processed events. This information provides a clear picture of your system’s security and operational status. Additionally, the Dashboard Menu offers seamless navigation to other related dashboards. This intuitive feature ensures a user-friendly experience, allowing you to effortlessly explore specific event categories and delve deeper into the nuances of your Windows environment. With Logstail, monitoring and analyzing your Windows endpoints becomes not only comprehensive but also incredibly convenient, enabling you to maintain a vigilant stance on security and performance.
Infrastructure Dashboard
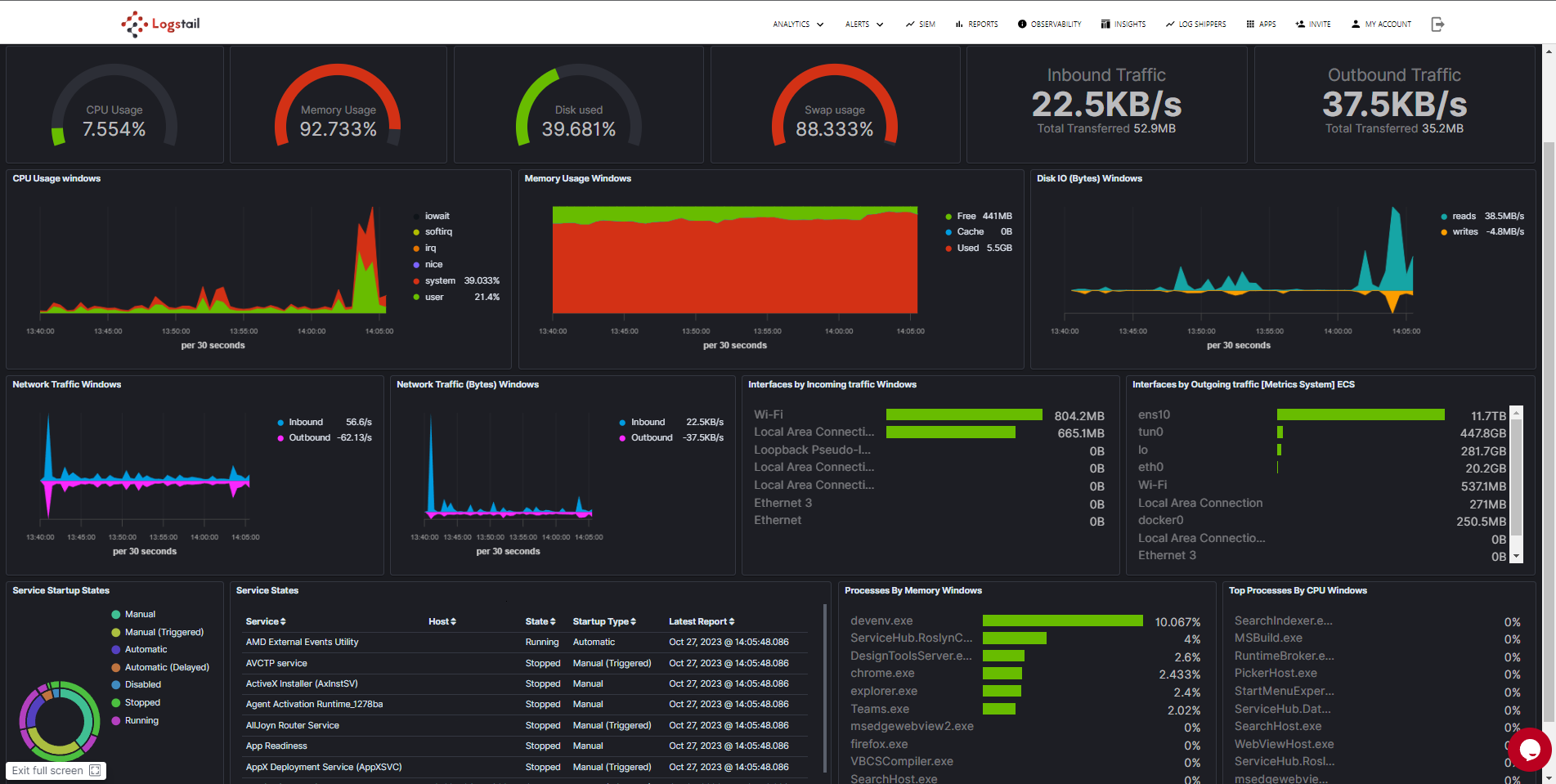
The infrastructure dashboard offers a comprehensive overview of the metrics collected from your Windows Endpoint. This powerful tool provides a holistic perspective, allowing you to monitor essential parameters such as CPU usage, Disk and Memory utilization, as well as inbound and outbound network traffic. Additionally, the dashboard enables you to meticulously track all running services and identify non-operational services, offering a detailed snapshot of your system’s performance and health. With this in-depth insight, you can proactively manage your Windows environment, ensuring optimal resource allocation, addressing potential bottlenecks, and swiftly resolving any service-related issues. Logstail’s infrastructure dashboard empower you to make data-driven decisions, enhancing the efficiency and reliability of your Windows systems.
Security Dashboard
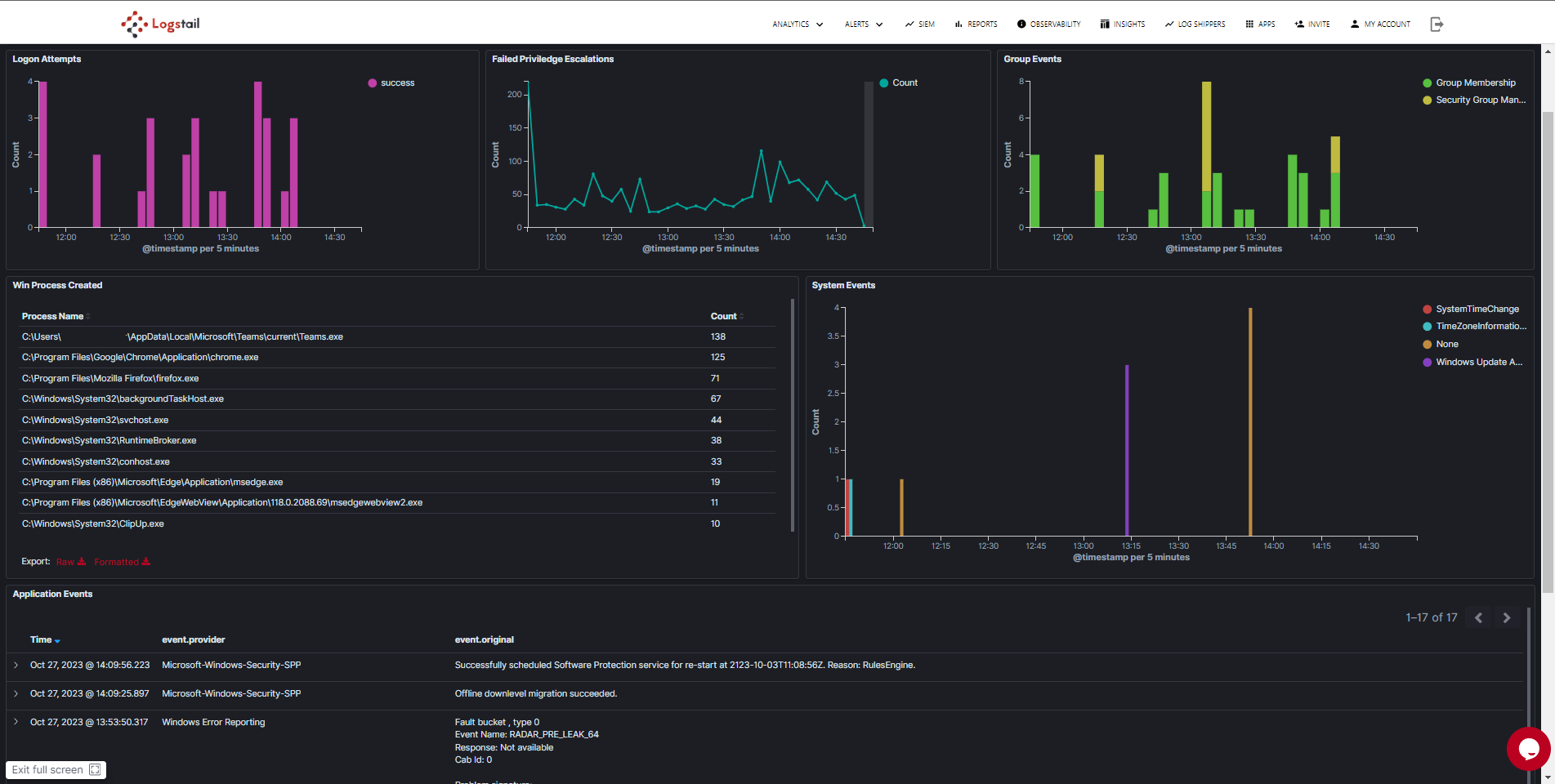
Within the Security Dashboard of Logstail, you’ll discover a wealth of critical insights presented in a visually intuitive manner. A dynamic timeline provides a clear overview of both failed and successful logins, enabling you to identify patterns and potential security threats. Additionally, there’s a dedicated visualization showcasing Privilege Escalation attempts, shedding light on any unauthorized access attempts to higher-level privileges. Another essential feature is the Group Events visualization, offering a comprehensive view of group-related activities within your system.
Furthermore, the Security Dashboard provides detailed information about created processes, along with System and Application events. This comprehensive overview allows you to monitor every aspect of your system’s activities, ensuring that you can promptly detect any suspicious behavior and swiftly respond to security incidents. Logstail’s Security Dashboard equips you with the tools needed to maintain a proactive security posture, offering both a high-level summary and granular details essential for robust security management.
Network Dashboard
This Dashboard is not related with the network collector described above. This provides a limited view to network connections. See the network collector dashboard below for more information!
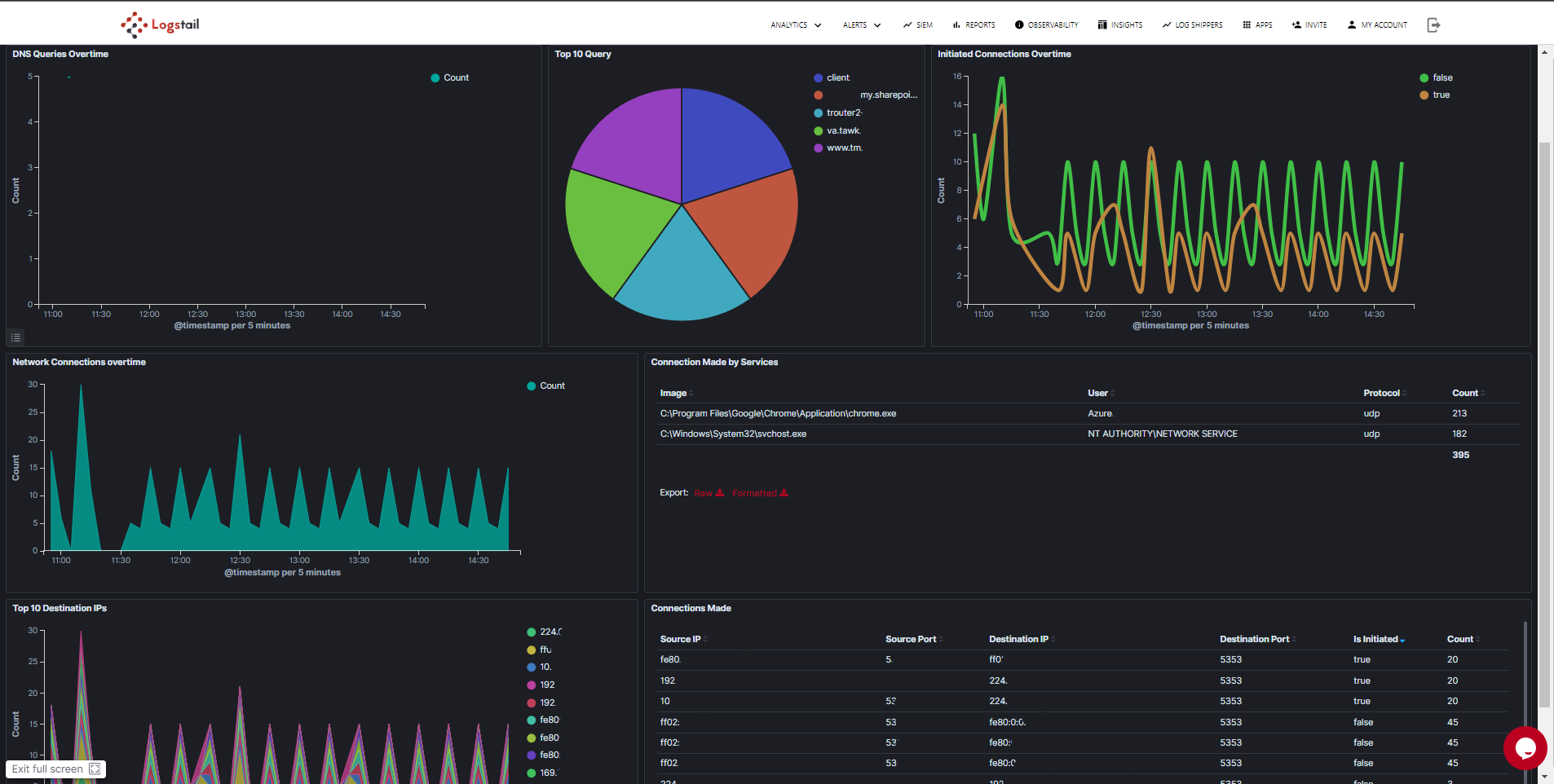
Within the network dashboard of Logstail, you gain a detailed understanding of the network activities originating from your Windows Endpoint. This insightful tool allows you to observe network connections and DNS queries made by your system. Crucial details, including source IP, source port, destination IP, destination port, and communication protocol, are provided for each connection. This granular information equips you with a comprehensive view of your network traffic, enabling you to identify potential security threats, monitor data exchanges, and ensure network efficiency. With Logstail’s network dashboard, you have the power to proactively manage your network infrastructure, making informed decisions to enhance both security and performance across your Windows environment.
PowerShell Dashboard
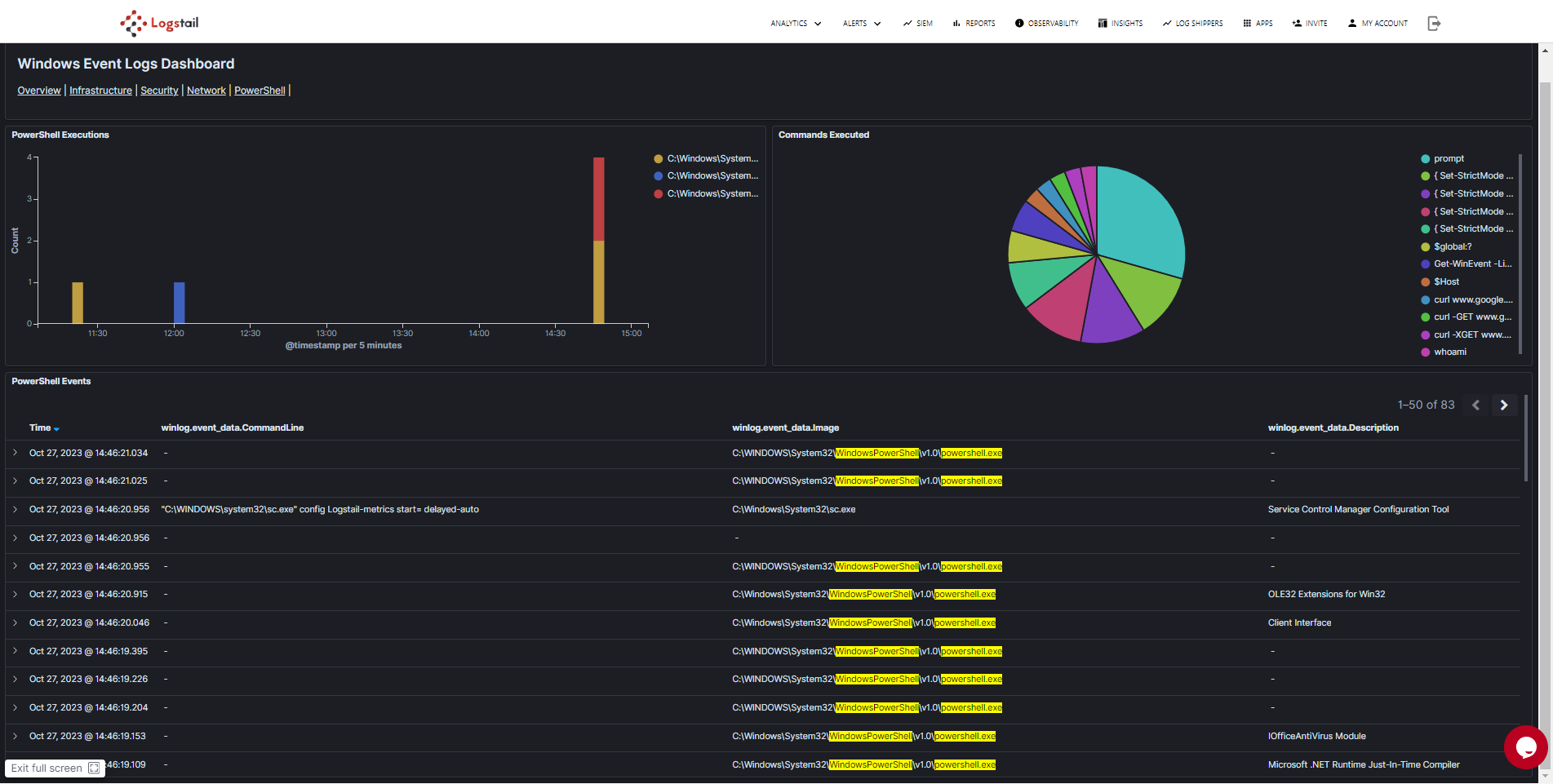
The Logstail PowerShell dashboard offers a visual representation of executed queries, empowering users to gain insights into the intricacies of PowerShell scripts. It provides a unique opportunity to explore all background processes associated with executed PowerShell scripts. This level of visibility is invaluable, allowing users to track script activities comprehensively, identify potential security threats, and ensure the integrity of their system. With Logstail, not only are queries visualized for easy analysis, but users can also uncover the underlying processes, enhancing their ability to monitor, analyze, and secure their Windows environment effectively.
Network Collector
As previously highlighted, Logstail offers the ability to install the Network Collector within the Logstail Agent. This integration provides unparalleled visibility and in-depth analytics regarding the network traffic of your Windows endpoint. By leveraging this capability, you can monitor network activities with precision, identifying patterns, potential vulnerabilities, and ensuring optimal bandwidth utilization. This granular insight equips you with the tools to enhance network security, troubleshoot issues promptly, and optimize the overall performance of your Windows environment. Logstail’s Network Collector redefines how you perceive and manage network traffic, offering a robust solution for maintaining a secure and seamlessly functioning Windows infrastructure.
You can learn about the data collected from the Network Collector and its related pre-built dashboards here.
Search Data with Logstail Discover Feature
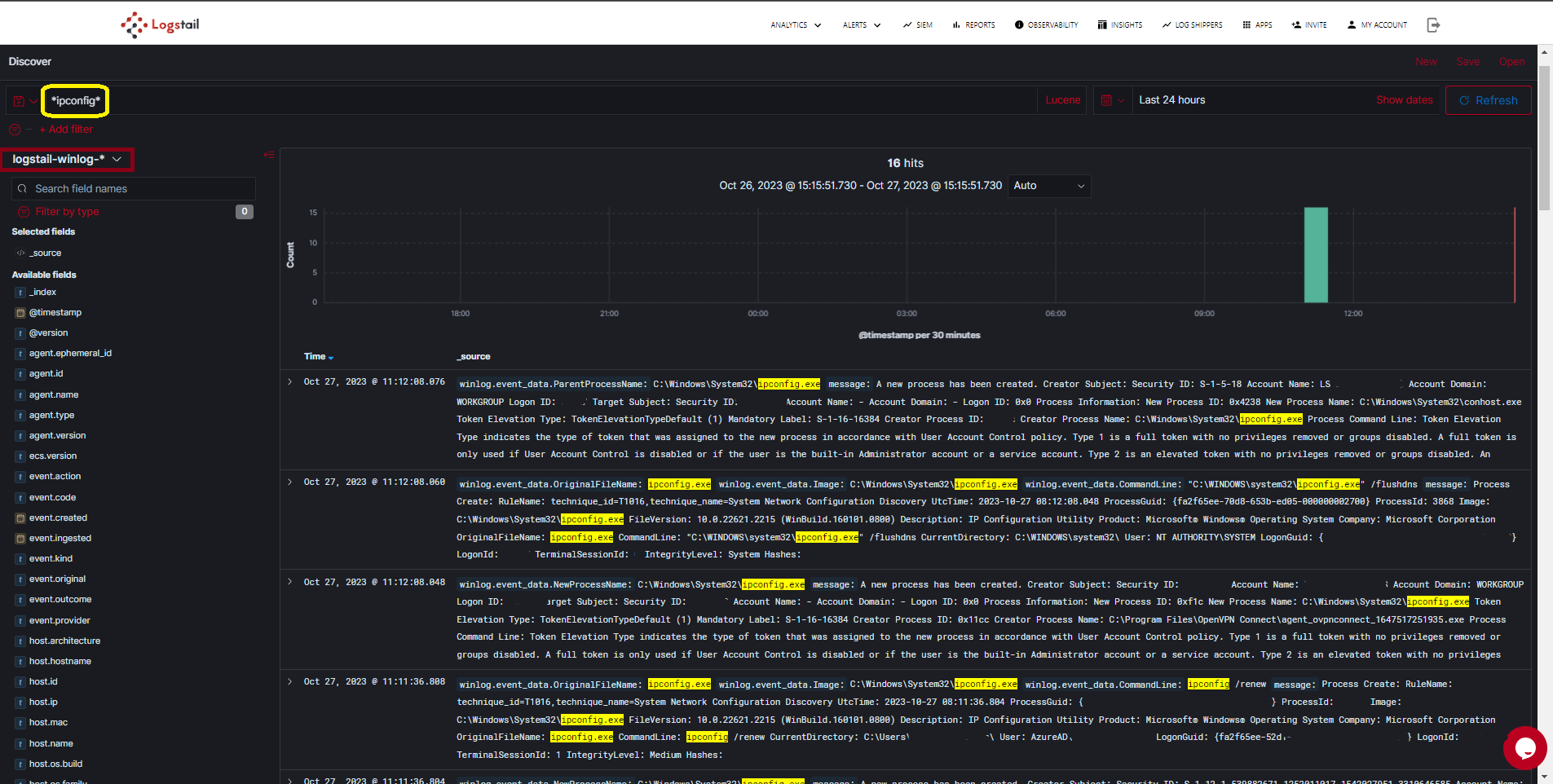
Logstail Discover Feature is a powerful and intuitive tool designed to unravel the depths of data within your collected data. It serves as a sophisticated search and analytics interface, enabling users to explore vast datasets effortlessly. With Logstail Discover, users can dig into their data, visualize trends, and uncover valuable insights in real-time. Its user-friendly interface allows for the seamless exploration of indices, fields, and documents, making it an essential tool for data analysts, researchers, and developers. This tool not only simplifies the process of data discovery but also facilitates advanced querying, filtering, and aggregation, providing users with a comprehensive view of their data landscape. Navigate to Analytics → Discover from Top Navigation menu to access the Discover Feature.
Select the logstail-winlog-* index at top left to view your Windows Endpoint collected data.
By harnessing the power of Logstail Discover, you can precisely search for specific events within your Windows Events data. For instance, you can effortlessly query events related to specific commands, such as “ipconfig.” This advanced search functionality provides a targeted approach to analyzing your Windows environment. With Logstail Discover, you gain the ability to delve deep into your event data, allowing you to uncover specific actions, troubleshoot issues, and monitor specific commands or activities across your Windows endpoints. This precision in searching enhances your overall visibility and control, ensuring that you can swiftly identify, analyze, and respond to events that matter most to your organization’s security and operational efficiency.
Generate Reports using Logstail Reporting Feature
Logstail’s Reporting feature offers a robust solution for transforming the wealth of data collected from Windows endpoints into actionable insights. With this feature, generating comprehensive reports becomes seamless and efficient. Logstail allows users to effortlessly create detailed reports based on the data displayed on dashboards, providing an organized summary of key metrics, events, and trends within the Windows environment. This reporting capability not only simplifies the process of data analysis but also enhances communication and decision-making within an organization. Whether it’s analyzing the success rates of specific operations, tracking security incidents, or monitoring resource utilization, Logstail’s Reporting feature enables users to customize reports to meet specific requirements. These reports, presented in clear and visually appealing formats, empower businesses to make informed decisions, track performance over time, and bolster security measures effectively. With Logstail Reporting, businesses can transform raw data into actionable intelligence, paving the way for smarter, data-driven strategies.
You can read more about Reporting Feature and learn how to generate reports in our extended guide.
Enhance security and performance with instant alerts
Configuring alerts based on triggers and receiving notifications for events through Logstail’s Alerting Feature is instrumental in maintaining the integrity and security of Windows logs and metrics. In today’s fast-paced digital landscape, where every second counts, timely detection and response to critical events are paramount. Logstail’s Alerting Feature allows users to set up customized triggers based on specific thresholds or patterns within Windows logs and metrics. For instance, detecting an unusual spike in CPU usage or multiple failed login attempts can trigger alerts. These alerts, sent in real-time notifications, enable IT professionals to promptly address potential issues, preventing downtime, data breaches, or system failures. The importance of alerting lies in its proactive nature, allowing organizations to identify anomalies, security breaches, or performance bottlenecks before they escalate into major problems. It empowers IT teams to respond swiftly, minimizing the impact on operations and ensuring the continuous and secure functioning of Windows-based systems. Ultimately, Logstail’s Alerting Feature not only safeguards data and systems but also enhances overall operational efficiency by enabling rapid, targeted responses to emerging events and threats.
You can read more about Alerting Feature and learn how to setup alerts in our extended guide.
Find abnormal patterns in your data
Logstail’s Insights Feature, centered around anomaly detection, stands as a pivotal tool in the realm of Windows endpoint monitoring. Anomalies, deviations from the expected patterns or behaviors, can often signify impending issues, security breaches, or inefficiencies within a system. Logstail’s Anomaly Detection feature harnesses advanced algorithms to identify these deviations in real-time, allowing IT professionals to swiftly pinpoint irregularities in Windows endpoint logs and metrics. This proactive approach is paramount in cybersecurity and system optimization. By recognizing unusual patterns, such as unexpected login activities, irregular resource usage, or unauthorized access attempts, organizations can detect and mitigate threats before they escalate. The significance of anomaly detection in Windows endpoint monitoring lies in its ability to provide early warnings, enabling rapid response, reducing downtime, and fortifying the overall security posture. With Logstail’s Insights Feature, businesses can stay one step ahead, ensuring the seamless operation and safeguarding of their Windows environments.
You can read more about Insights Feature and learn how to setup anomaly detectors in our extencded guide.
Conlusion
In conclusion, Logstail emerges as the linchpin in the realm of Windows endpoint monitoring, offering a comprehensive suite of features designed to enhance security, optimize performance, and provide invaluable insights. By seamlessly integrating with Windows environments, Logstail empowers organizations to collect, analyze, and act upon crucial data from logs and metrics. From real-time event tracking and anomaly detection to intuitive dashboards and proactive alerting, Logstail ensures that IT professionals have the tools they need to maintain the integrity and security of their Windows endpoints. Through its user-friendly interface, customizable reporting, and advanced features, Logstail not only simplifies the complexities of monitoring but also equips businesses with the agility to respond swiftly to emerging threats and operational challenges. With Logstail at the helm, businesses can navigate the digital landscape with confidence, ensuring the continuous and secure operation of their Windows-based systems.
Contact Our Experts or Sign Up for Free